Innovation
ConnectGuard™ MACsec authentication and encryption
Ethernet networks are the foundation of modern IT infrastructures. In distributed environments with sensitive data and a high degree of automation, the demand for consistent, high-performance encryption is increasing. ConnectGuard™ MACs ...
Learn more

Post-quantum cryptography (PQC)
The computational power of emerging quantum computers poses a threat to many classical cryptographic systems. Public key cryptography and signature algorithms that are currently in use are no longer secure ...
Learn more

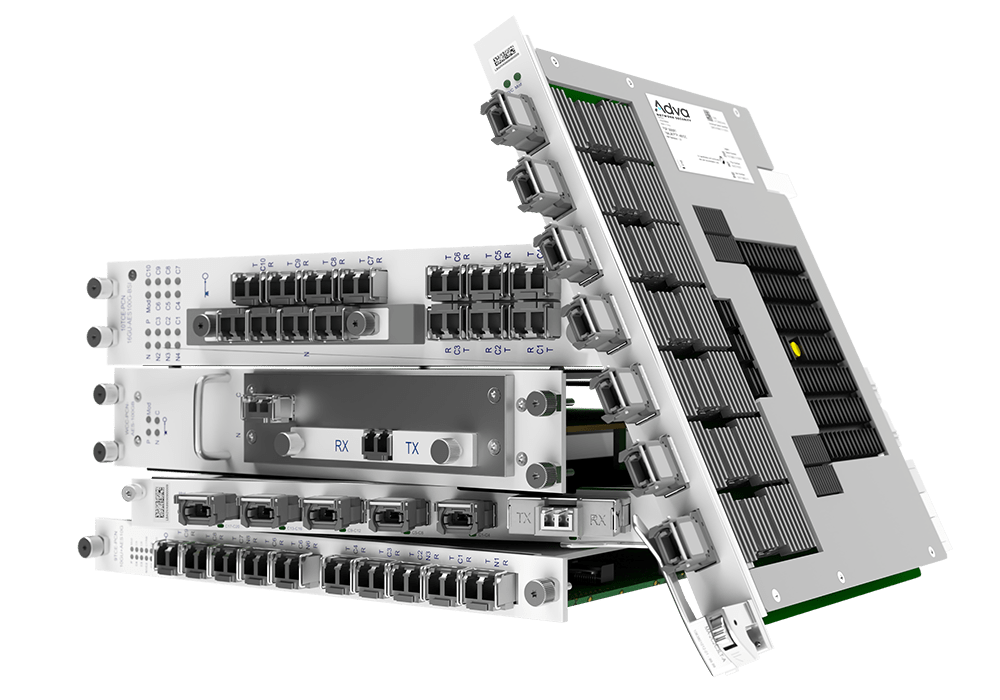
Layer 1 encryption
Fiber-based high-speed communication networks are crucial for essential services, governments and defense, as they transport huge amounts of mission-critical data ...
Learn more

Integrated virtualization
Integrated virtualization makes it possible to embed security-related network functions directly into existing infrastructure without external systems or additional hardware ...
Learn more
Mission-critical networks
Information security is a major challenge for critical infrastructure and operators of essential services. Established protection mechanisms are increasingly at risk ...
Learn more

Secure cloud infrastructure
Increasing cyber risks pose a significant threat to critical infrastructures, public authorities and businesses. In this digital era, highly secure and efficient networks ...
Learn more

Quantum Key Distribution (QKD)
The privacy and integrity of communication relies on secret keys. Key-establishment mechanisms use asymmetrical ciphers and algorithms like RSA and Diffie-Hellman ...
Learn more